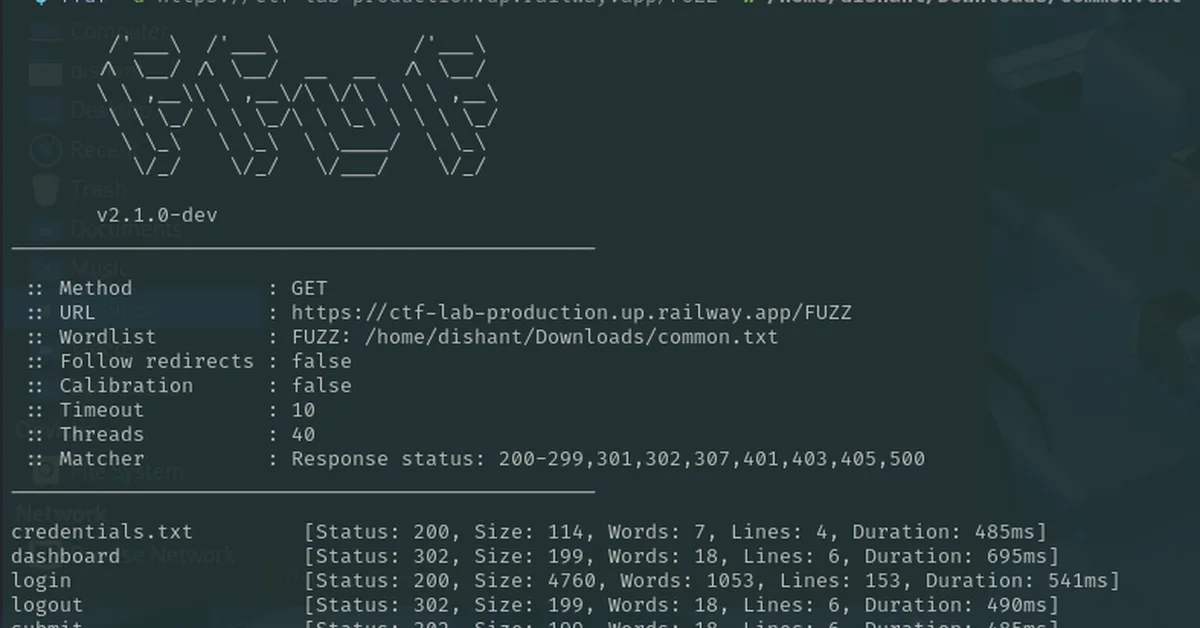
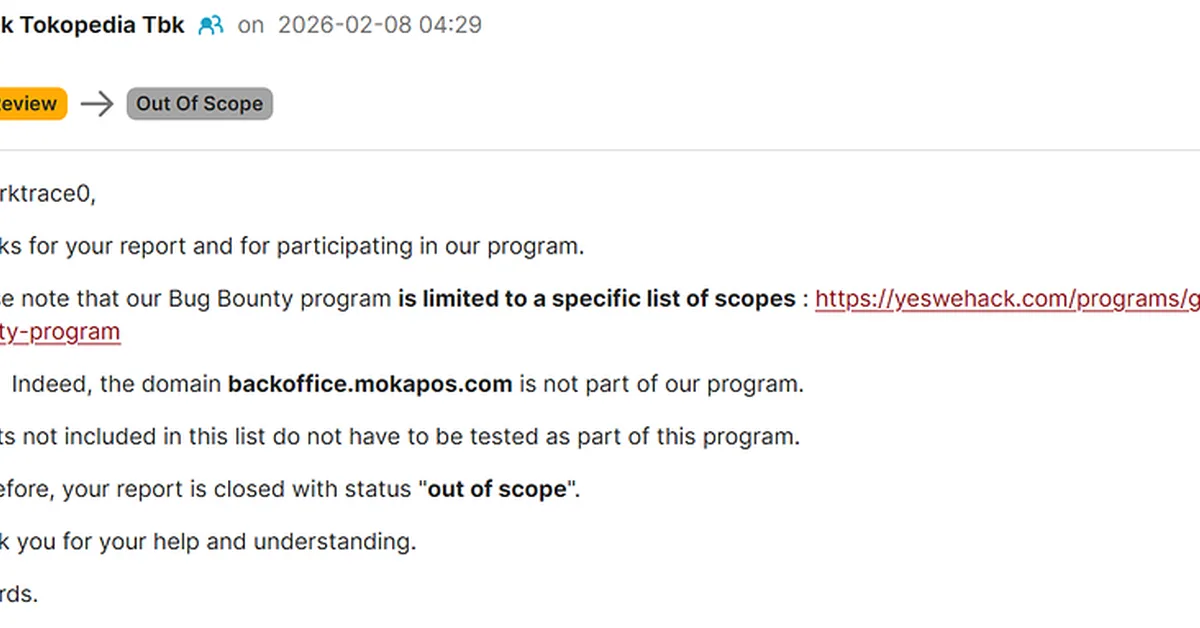
The article provides a step-by-step walkthrough of a web pentesting CTF challenge that involves chaining vulnerabilities like IDOR and SQL injection to gain access to admin panels and retrieve flags. It highlights the importance of methodical testing and understanding different attack vectors for content creators looking to enhance their cybersecurity skills.
Read the full article at InfoSec Write-ups - Medium
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.