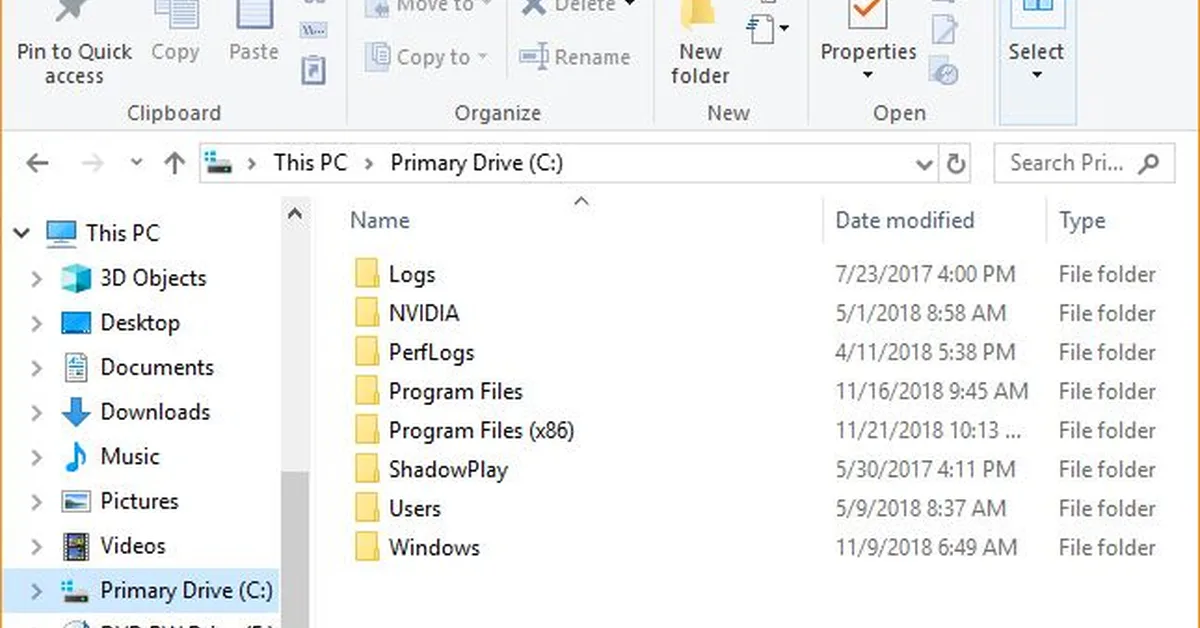
WebDAV is exploited by threat actors to deliver malware via Windows File Explorer, tricking victims into believing files are local rather than remote. This tactic involves using URL shortcut (.url) and LNK files to open WebDAV links that appear safe but actually download malicious scripts or executables from controlled servers. Pop-up warnings in File Explorer can be easily ignored by users, leading to successful execution of payloads like XWorm RAT, Async RAT, and DcRAT. German language finance-themed emails are the most common vector for this attack, followed by English language campaigns.
Read the full article at Cofense
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.