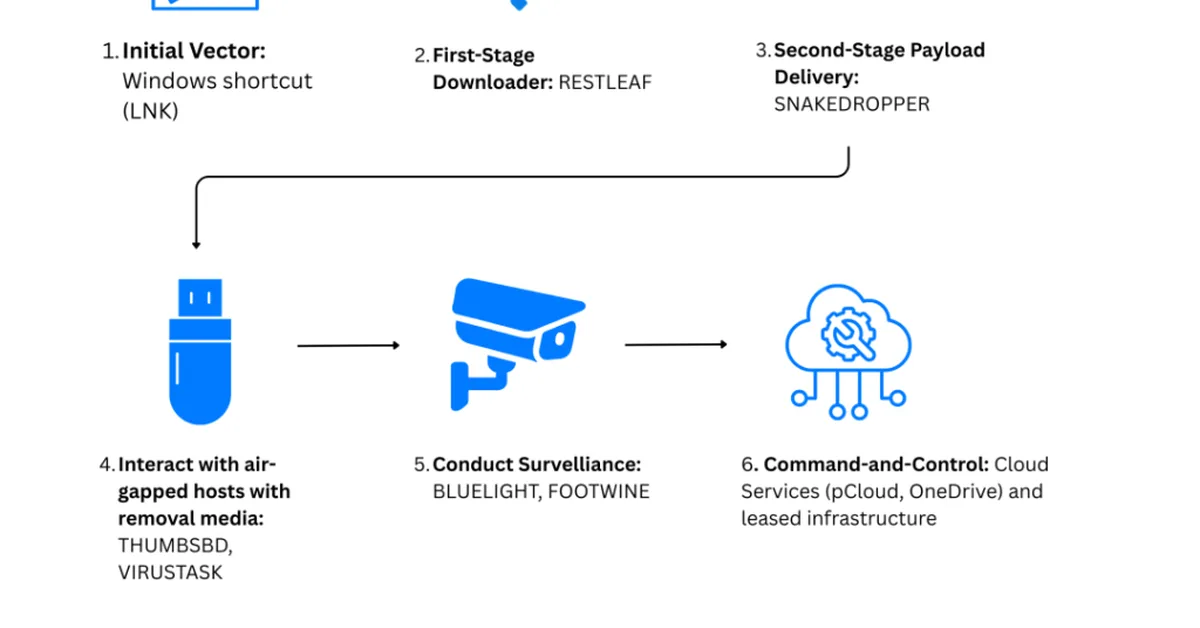
North Korea-linked APT37 used Zoho WorkDrive and USB-based malware in a campaign called Ruby Jumper to infiltrate air-gapped systems, deploying tools like RESTLEAF and SNAKEDROPPER for surveillance and data exfiltration. This highlights the evolving threat landscape where attackers leverage cloud services and physical media to breach isolated networks, underscoring the need for enhanced endpoint security measures.
Read the full article at Security Affairs
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.