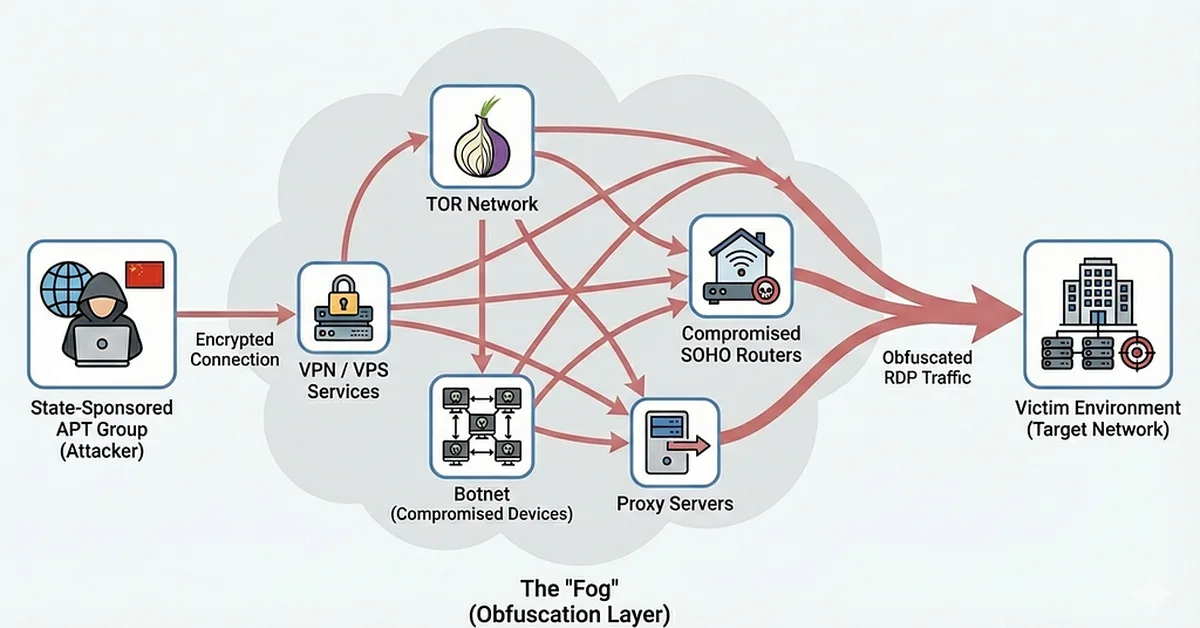
The article discusses how traditional network-based detection methods for identifying compromised RDP sessions are becoming less effective due to attackers using advanced obfuscation techniques. It highlights the importance of analyzing application-layer metadata from RDP clients, such as keyboard layout and timezone, which remain consistent even when traffic is encrypted or routed through proxies. Content creators should focus on developing anomaly-based detection systems that identify deviations in these metadata signals to uncover hidden threats.
Read the full article at Malware Analysis, News and Indicators - Latest topics
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.