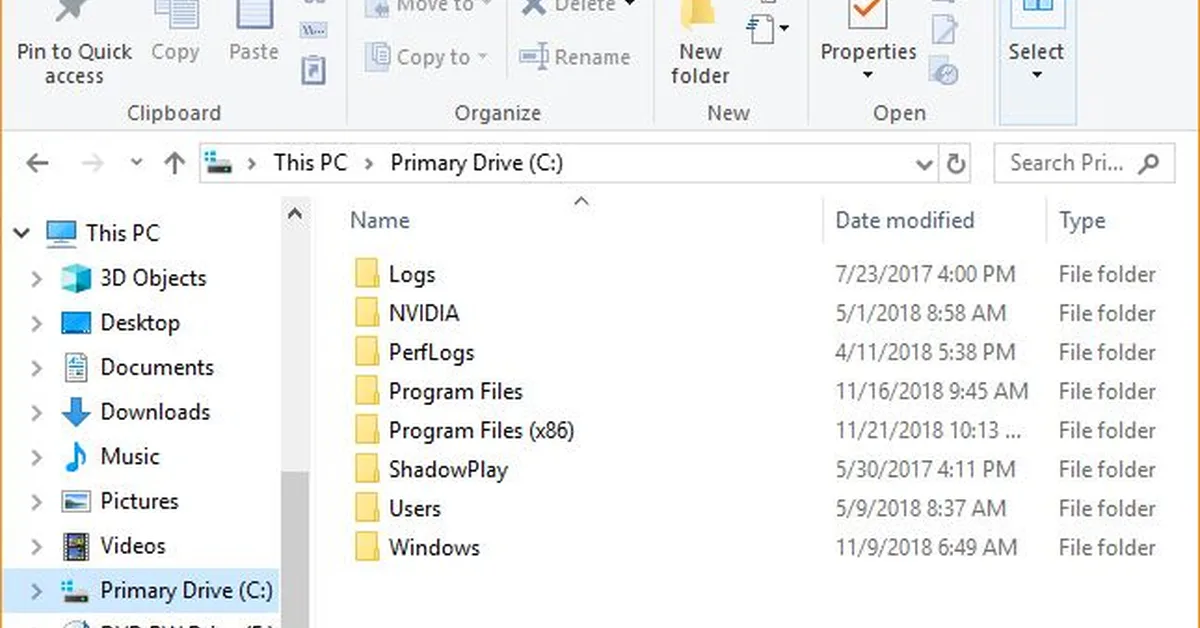
The analysis involves a memory dump from a system infected with malware, focusing on two suspicious files: LiDseDHx.exe and qTbZGdHw.exe. The researcher uses Volatility for memory forensics, extracting strings and images of these files. Despite thorough examination including YARA rules and sandboxing, the exact nature and behavior of the malware remain unclear due to its dormant state in the analysis environment. Key findings include file paths, hashes, and potential indicators of compromise (IOCs) related to the suspicious executables and their associated libraries.
Read the full article at System Weakness - Medium
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.