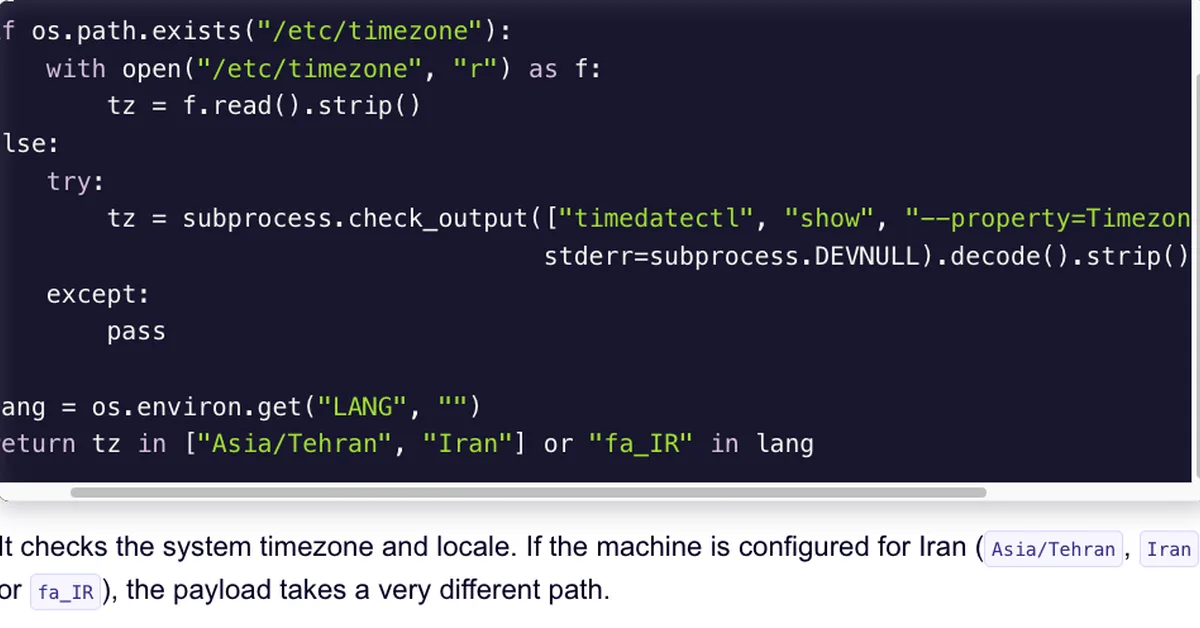
The research highlights that legitimate tools commonly used in enterprise environments can be abused for data exfiltration by leveraging existing trust relationships and normal operational patterns to obscure malicious activity. Key observations include: 1) Similarity of network traffic - Exfiltration often uses standard protocols like HTTPS, making it difficult to distinguish from authorized business activity at the network layer. 2) Variability of forensic artifacts - Some tools leave a rich footprint for incident response while others operate with little evidence beyond process execution and command-line telemetry. 3) Cloud-native tools blend into normal operations - Authentication flows and data transfer patterns during exfiltration closely resemble legitimate cloud usage, complicating detection efforts. The research emphasizes the need to correlate endpoint telemetry with network and cloud data for effective detection of exfiltration activities using legitimate tools.
Read the full article at Cisco Talos
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.