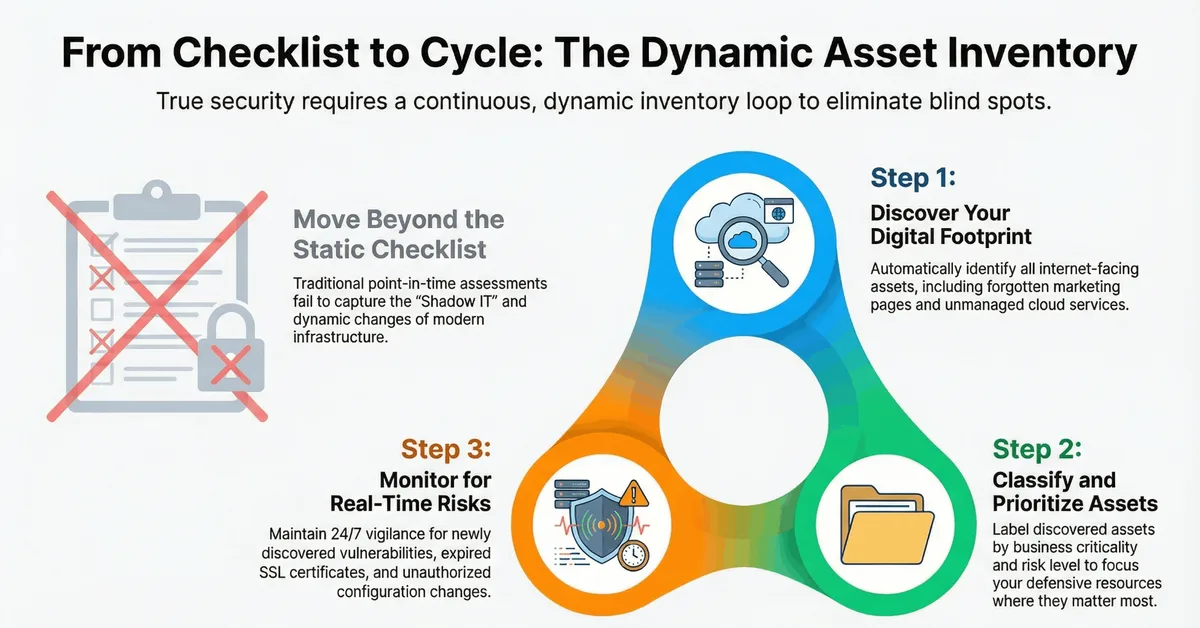
The article discusses the importance of creating a dynamic digital asset inventory in modern enterprises to address the expansive and complex attack surface beyond traditional perimeter security. It highlights that static methods like spreadsheets are inadequate due to the prevalence of Shadow IT and the constant evolution of digital assets. The key takeaway is adopting a continuous discovery, classification, and monitoring approach to ensure visibility and protection against threats.
Read the full article at SOCRadar-? Cyber Intelligence Inc.
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.