A threat actor exploited a supply chain attack to gain full AWS admin access within 72 hours, highlighting risks of permissive CI/CD trust relationships and underscoring the need for strict security measures like least-privilege policies and anomaly detection. Content creators should emphasize the importance of secure coding practices and robust monitoring systems to prevent such breaches.
Read the full article at AboutDFIR G?? The Definitive Compendium Project
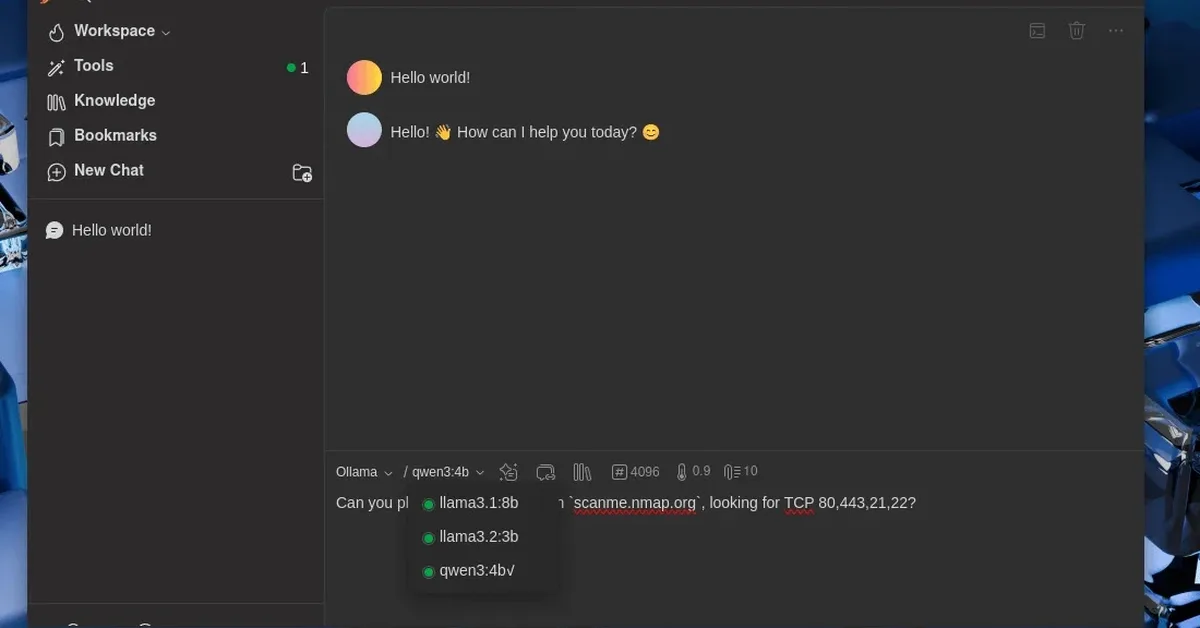
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.