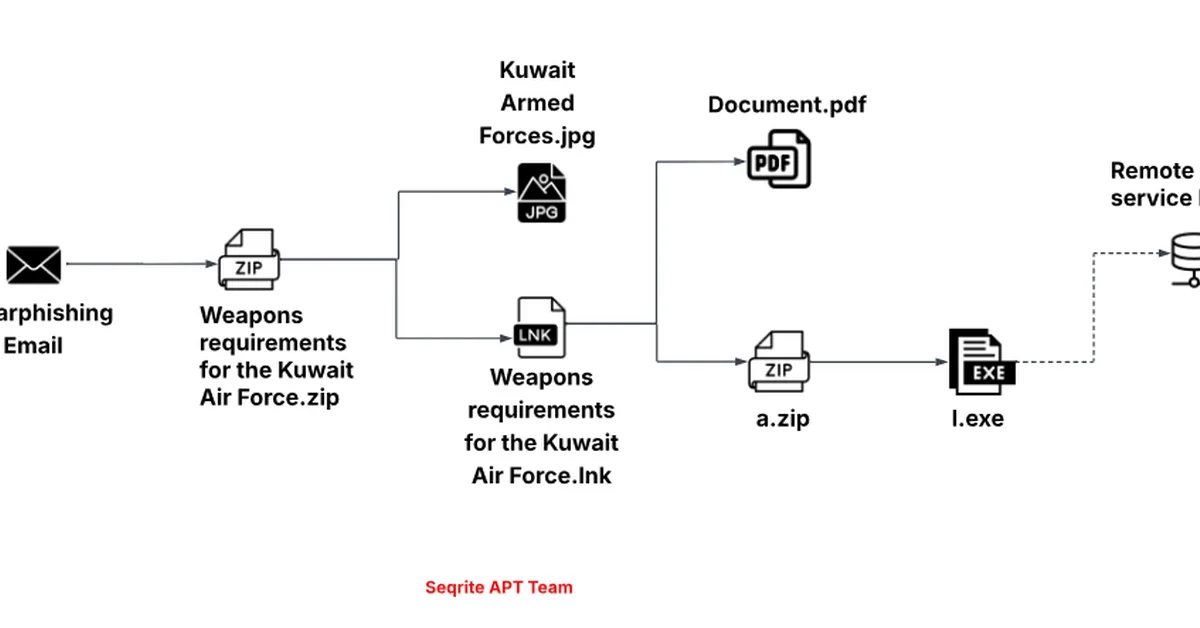
Seqrite Labs APT Team identified a multi-region espionage campaign targeting government and defense entities in Algeria, Mongolia, Ukraine, and Kuwait, leveraging decoy documents and malicious archives to deploy a JavaScript loader named HOPPINGANT for data exfiltration using Rclone. The campaign highlights the strategic importance of these countries amid regional tensions and underscores the need for content creators to emphasize cybersecurity measures against sophisticated phishing tactics.
Read the full article at Malware Analysis, News and Indicators - Latest topics
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.