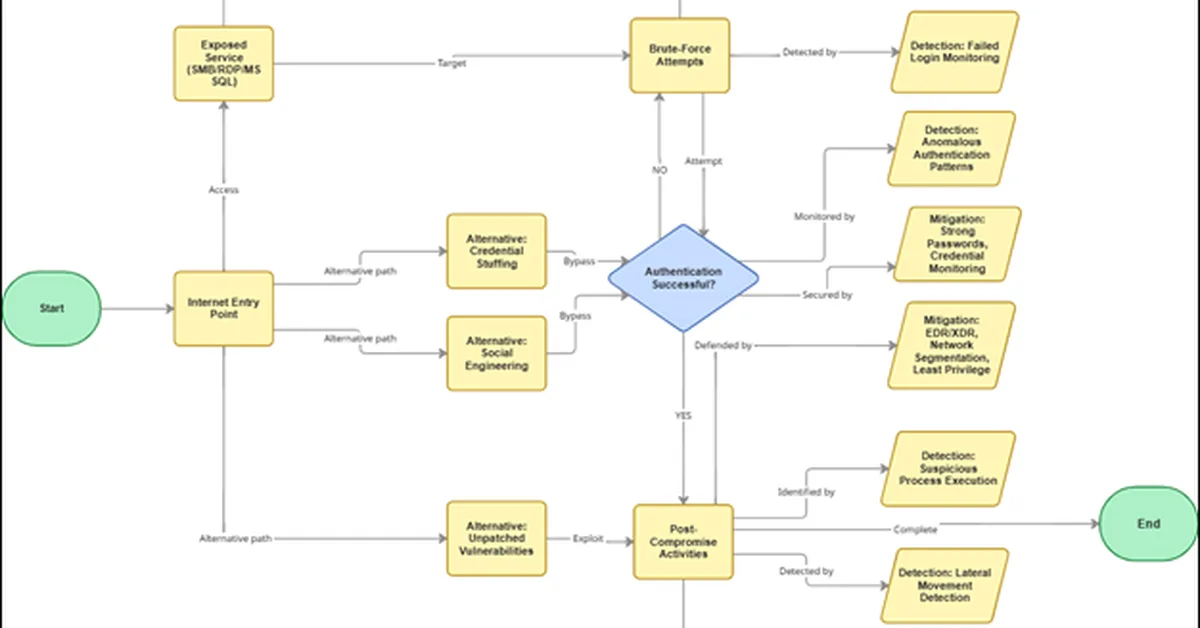
The article discusses secure communication protocols and their implementation, emphasizing that encryption alone is insufficient to prevent attacks like brute-force credential guessing. It highlights the importance of combining strong authentication, controlled network exposure, continuous monitoring, and incident response planning to enhance overall security posture. Content creators should focus on integrating these defensive strategies with secure protocol use to protect against real-world threats effectively.
Read the full article at Malware Analysis, News and Indicators - Latest topics
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.