This article highlights common security pitfalls in smart contract accounts and provides guidance to avoid them:
-
Signature Malleability: Ensure signatures are not malleable by using a canonical signing method that produces consistent results across different implementations.
-
Overestimating Validation Gas: Accurately estimate the gas required for signature validation within the account's execute function, avoiding underestimation which can lead to execution failures or overestimation leading to wasted resources and potential vulnerabilities.
-
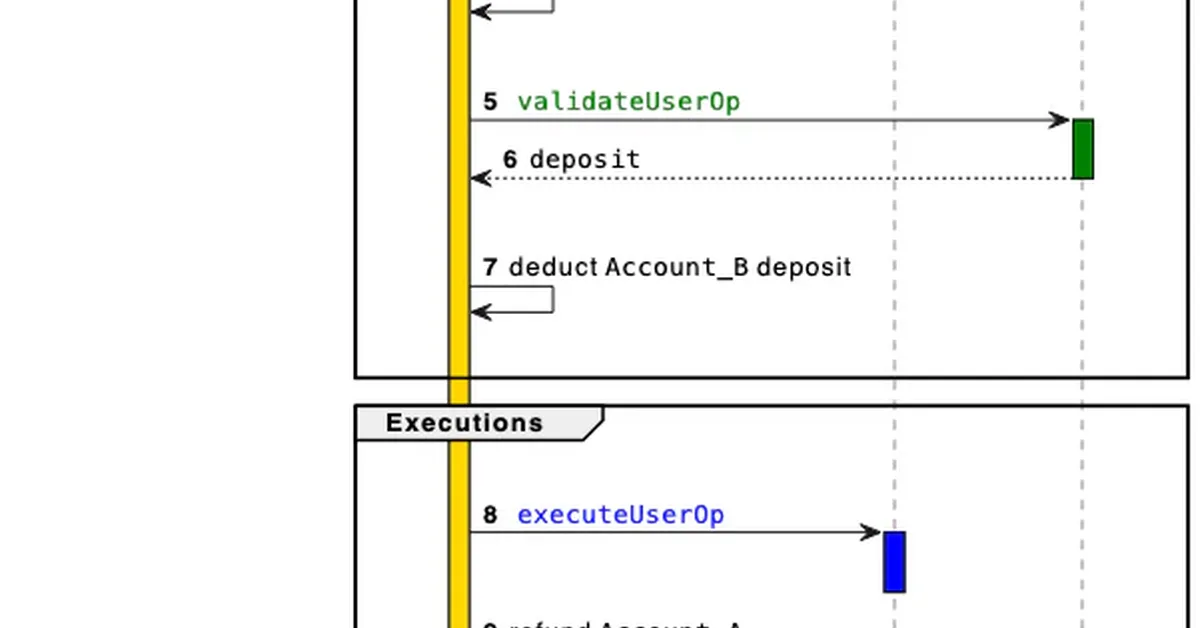
Batch Semantics Misunderstanding: Be aware that all validations run before any executions in batch operations, so temporary approvals written during validation phases can be overwritten by subsequent validations within the same batch.
-
ERC-1271 Replay Signature Attack: Prevent signatures from being reused across different accounts or networks by ensuring they are domain-separated with both the account address and chain ID through EIP-712 typed data.
Read the full article at Security Boulevard
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.