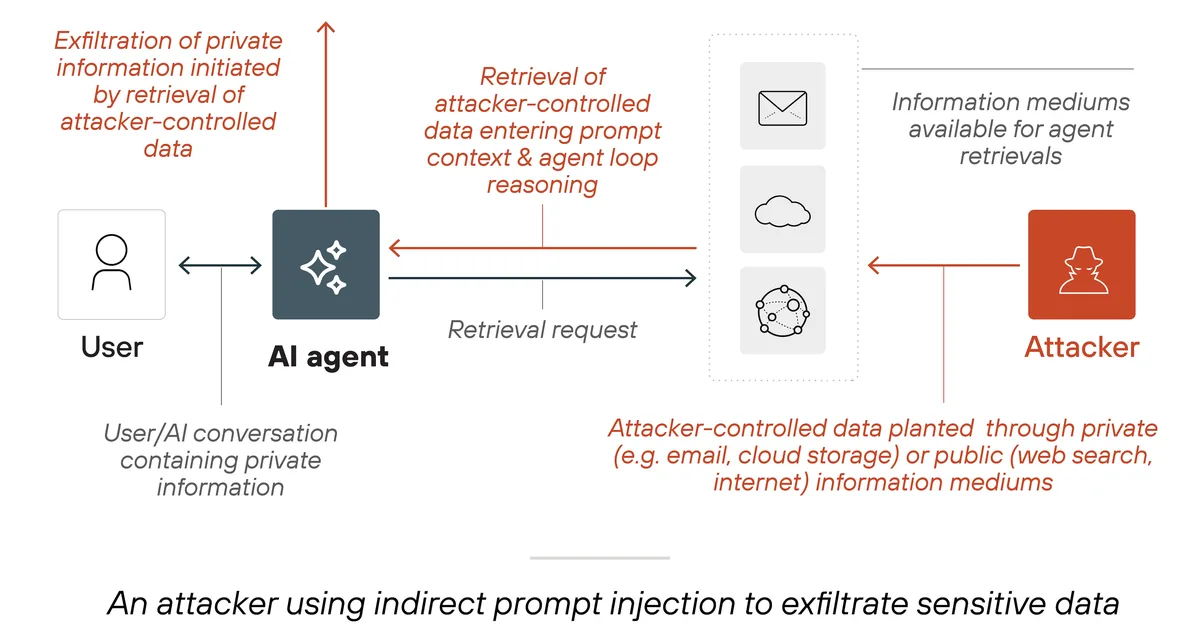
The article details a penetration testing scenario where an attacker gains access to a PDF file containing instructions and credentials for accessing an MSSQL database. Using these credentials, the attacker successfully connects to the database using Beekeeper Studio and begins enumerating its contents. The goal is to gather as much information as possible from the server, including user accounts, privileges, databases, tables, and potentially stored passwords or sensitive data.
Read the full article at InfoSec Write-ups - Medium
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.