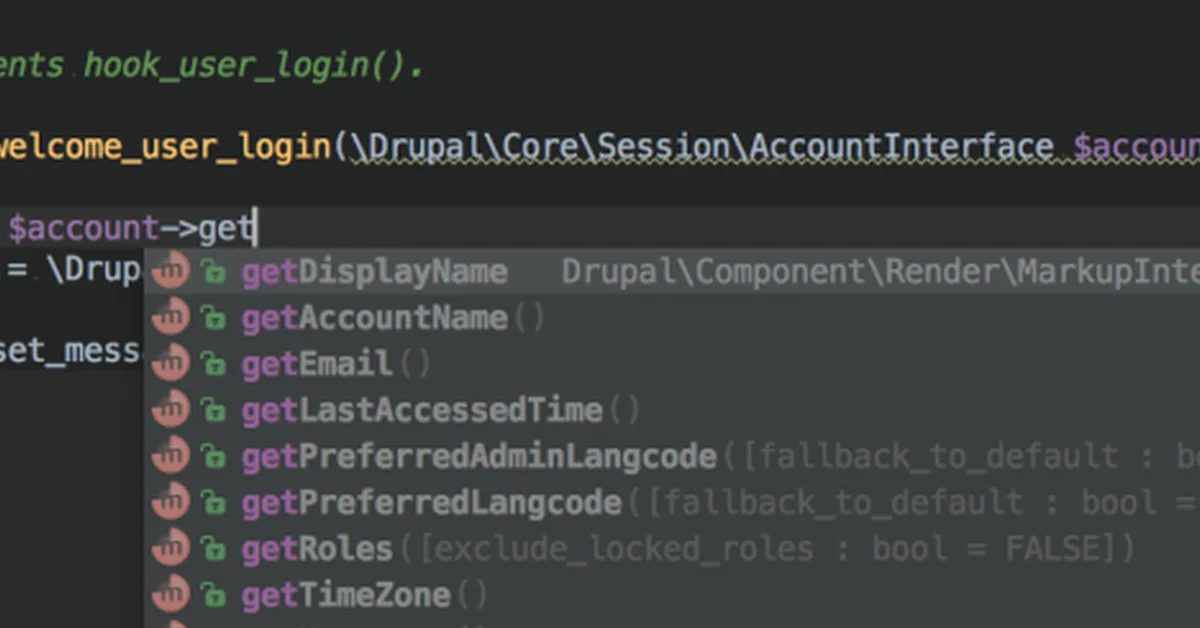
The article discusses how processes can inherit privileges from their parent process and explores methods to abuse capabilities for privilege escalation in Linux systems. Content creators should be aware of common tools that can be exploited, such as find, awk, and less, which can lead to unauthorized access if misconfigured.
Read the full article at DEV Community
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.