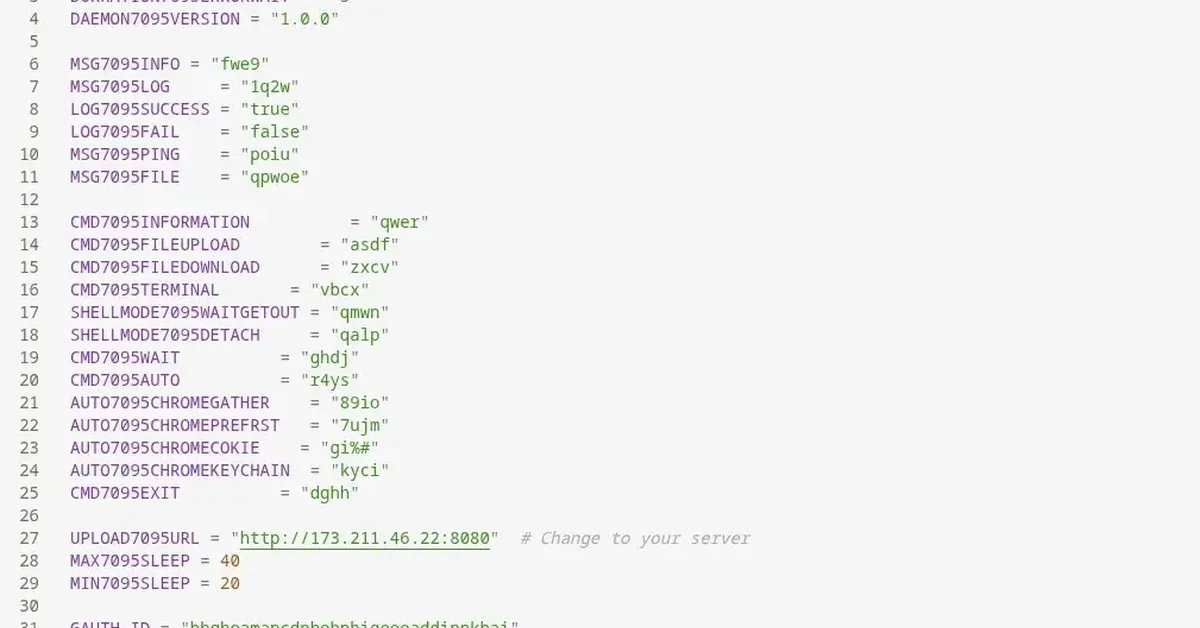
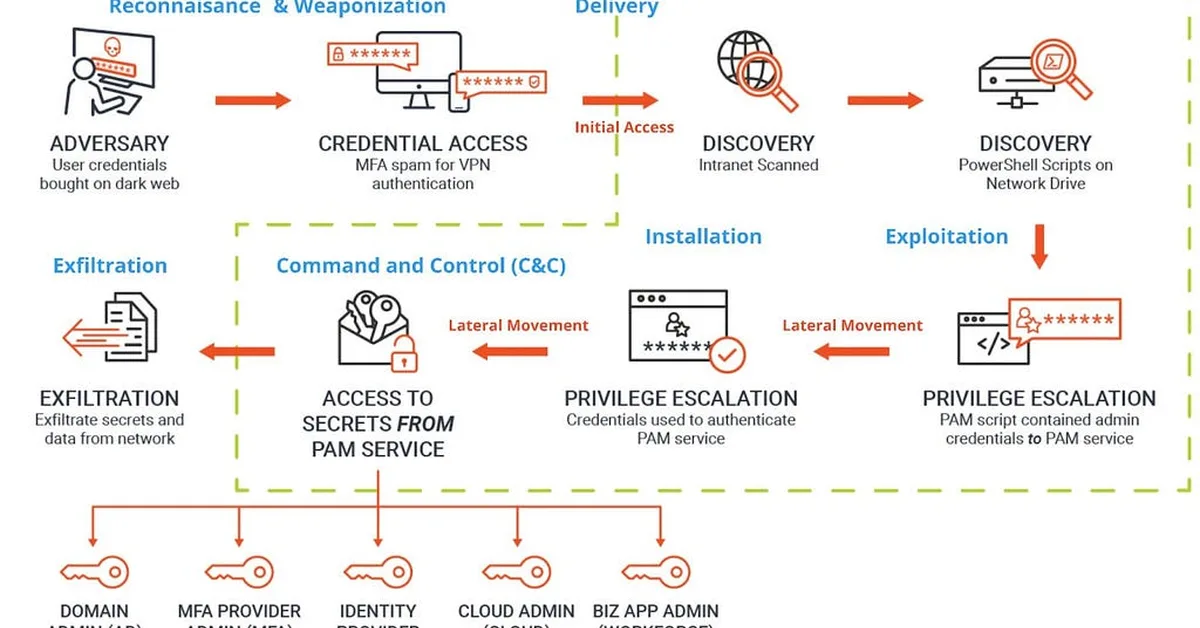
This write-up details a comprehensive walkthrough of an Active Directory (AD) penetration test scenario from zero credentials to full domain compromise. The process involves identifying the Domain Controller using RustScan and Nmap, exploiting guest SMB access for enumeration, cracking service account passwords via Kerberoasting, mapping permissions with BloodHound, password spraying, targeted kerberoasting, RDP exploitation, and finally obtaining a SYSTEM-level shell as a Domain Admin to capture the flag. Key takeaways emphasize the risks of default guest accounts, weak service account management, password reuse, hardcoded credentials in scripts, and bypassing restricted desktop environments.
Read the full article at InfoSec Write-ups - Medium
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.