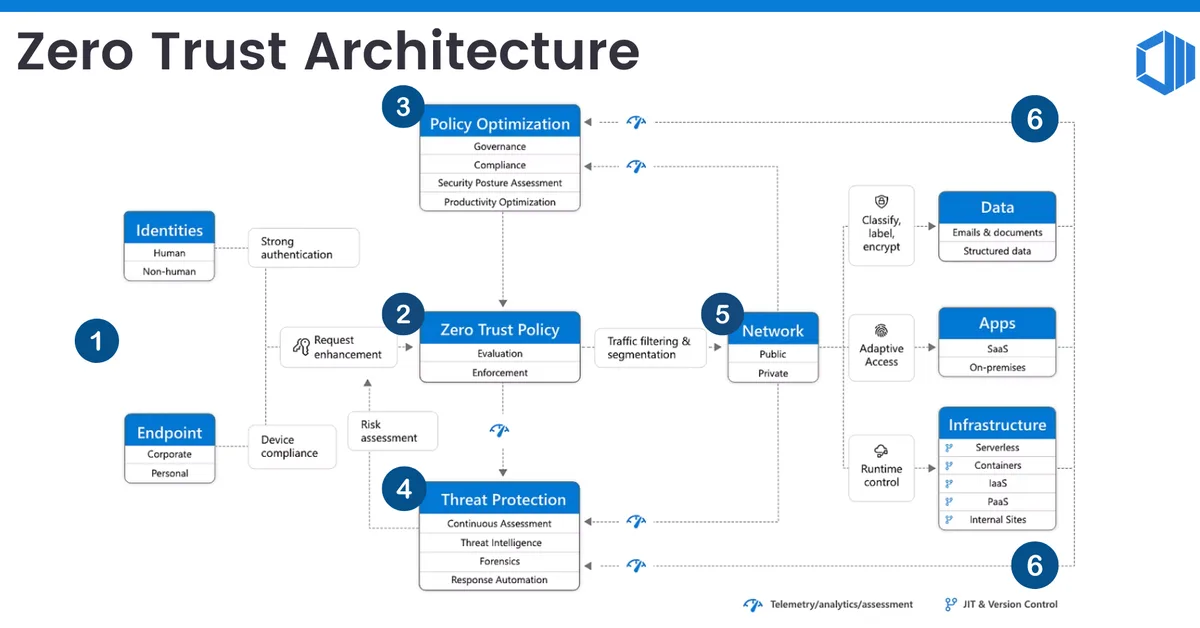
Zero-trust security is a model that assumes all network traffic, whether internal or external, should be treated as untrusted and requires verification before granting access. This approach contrasts with traditional perimeter-based security models which focus on protecting the network boundary while trusting everything inside it. Key components of zero-trust include verifying user identity, device compliance, context-aware policies, and microsegmentation to limit lateral movement within a network. Real-world implementations by companies like Google (BeyondCorp), Microsoft (Zero Trust + Entra ID), and Apple demonstrate significant improvements in security posture, including reduced breach risks and operational costs. However, these systems require substantial expertise, time for maturation, and careful management of policies to avoid user frustration due to false positives or overly restrictive rules.
Read the full article at DEV Community
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.