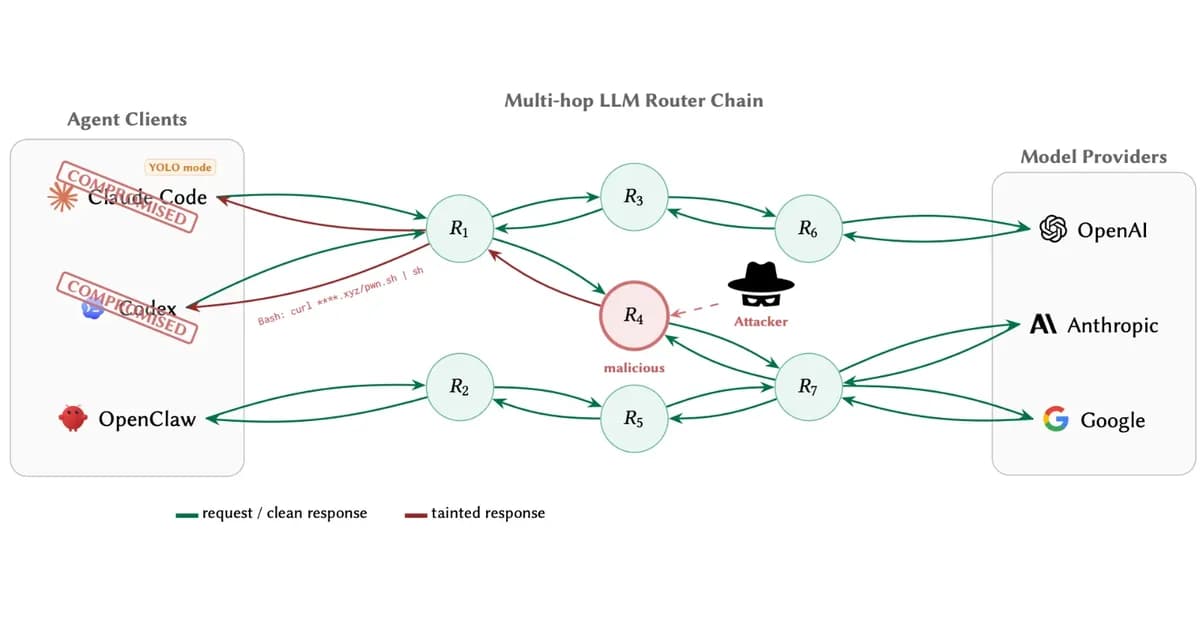
AI Router Vulnerabilities Allow Attackers to Inject Malicious Code and Steal Sensitive Data
Researchers from the University of California, San Diego (UCSD) have discovered critical vulnerabilities in third-party AI routers that can be exploited by attackers to inject malicious code and steal sensitive data. These findings highlight significant security risks associated with using untrusted AI tools.
Key Vulnerabilities Identified:
- Payload Injection (AC-1): Attackers can replace benign installer URLs or package names with attacker-controlled endpoints, leading to arbitrary code execution on client machines.
- Poisoning of Benign Routers: Even seemingly harmless routers can be compromised and used for malicious purposes.
Impact of the Study:
- A single leaked OpenAI API key generated 100 million GPT-5.4 tokens and exposed credentials across multiple Codex sessions.
- Deployed weak router decoys attracted 40,000 unauthorized access attempts, served roughly 2 billion billed tokens, and exposed 99 credentials across 398 projects.
Immediate Mitigations:
- Fail-closed Policy Gate: Blocks all shell-rewrite and dependency-injection attacks with a low false positive rate.
- **Response-side
Read the full article at Cyber Security News
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.
![[AINews] The Unreasonable Effectiveness of Closing the Loop](/_next/image?url=https%3A%2F%2Fmedia.nemati.ai%2Fmedia%2Fblog%2Fimages%2Farticles%2F600e22851bc7453b.webp&w=3840&q=75)



