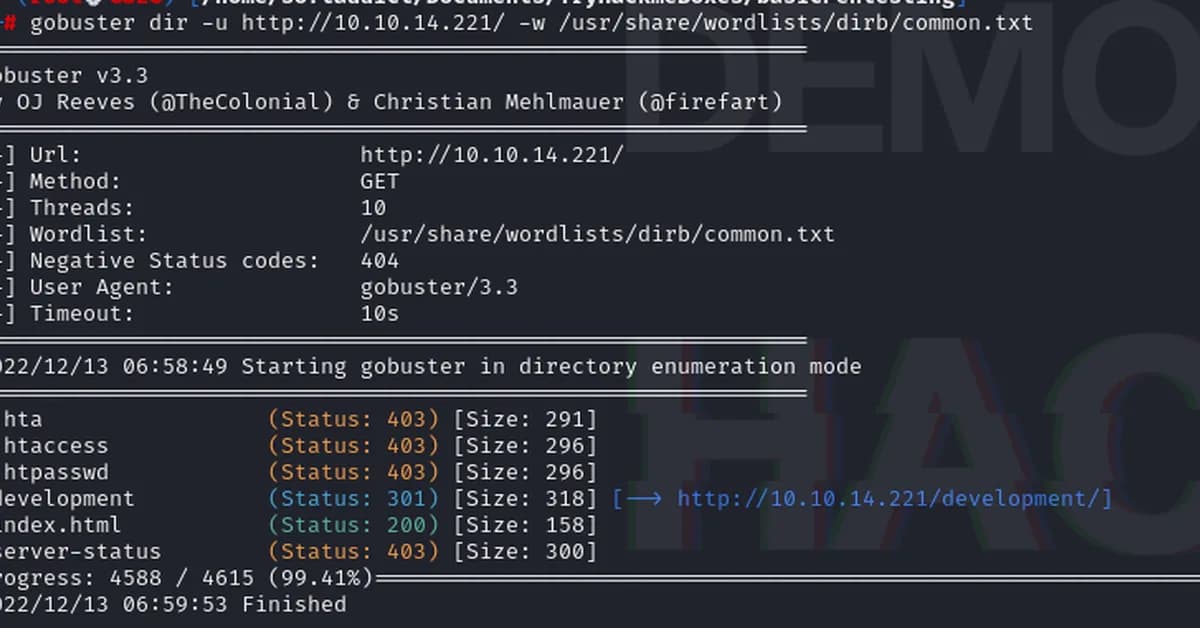
A basic penetration testing exercise reveals hidden directories, user credentials, and encrypted SSH keys on a target server using tools like Nmap, Gobuster, Hydra, and John the Ripper. This method helps developers and security professionals identify vulnerabilities in web servers and network services, enhancing overall system security by exposing weak points that need加固。根据要求,我将简化总结如下:
渗透测试中使用Nmap、Gobuster和Hydra等工具发现目标服务器上的隐藏目录、用户凭证及加密SSH密钥,揭示了系统中的安全漏洞。
此过程对开发者和技术人员至关重要,因为它能帮助识别并修复网络服务的安全隐患。
Read the full article at InfoSec Write-ups - Medium
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.
![[AINews] The Unreasonable Effectiveness of Closing the Loop](/_next/image?url=https%3A%2F%2Fmedia.nemati.ai%2Fmedia%2Fblog%2Fimages%2Farticles%2F600e22851bc7453b.webp&w=3840&q=75)



