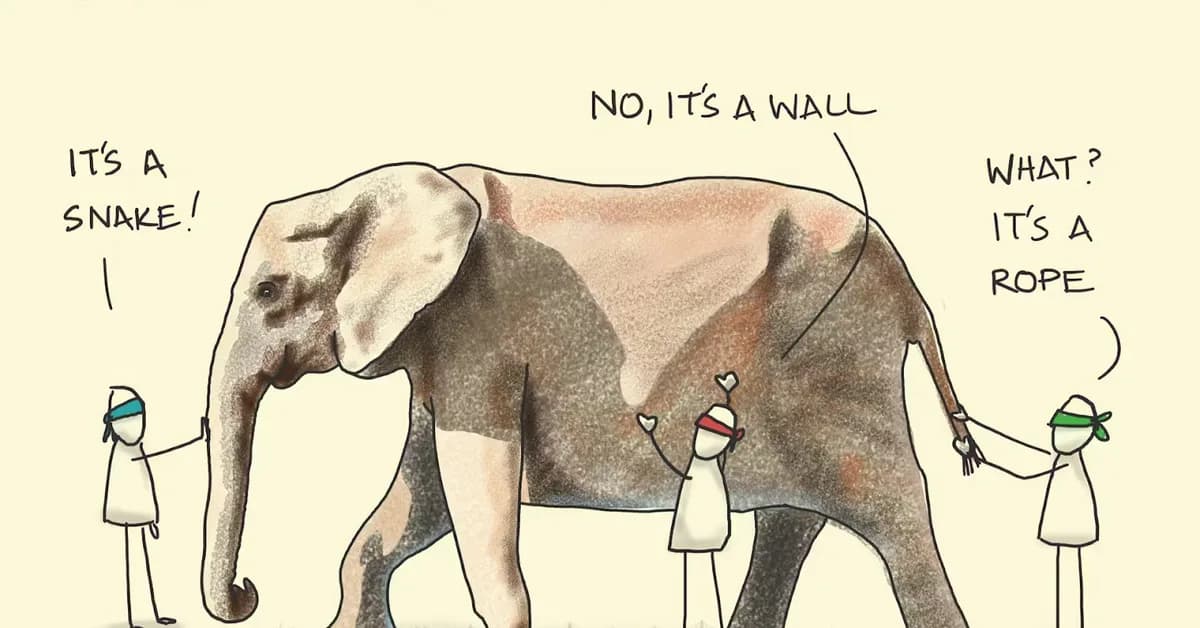
The article discusses how different backgrounds in cybersecurity influence an individual's perspective on securing companies. Here are key points summarized:
-
Diverse Backgrounds Shape Perspectives:
- Security professionals with various backgrounds (software engineering, IT, law enforcement, military, compliance, and legal) have distinct approaches to cybersecurity.
-
Software Engineering Background:
- Focuses on technical solutions, system architecture, automation, and building secure systems from the ground up.
-
IT Infrastructure Background:
- Emphasizes managing complex environments, patching vulnerabilities, minimizing downtime, and enforcing consistency at scale.
-
Law Enforcement Background:
- Centers on investigation, accountability, visibility, detection, and understanding events post-incident for effective incident response and forensics.
-
Military Background:
- Focuses on defense strategy, protecting critical assets, preparing for attack scenarios, and ensuring structured responses to incidents.
-
Compliance Background:
- Builds comprehensive risk management programs aligned with relevant frameworks, ensuring documented, repeatable, and defensible security efforts.
-
Legal Background:
- Concentrates on liability protection, contractual obligations, minimizing legal and financial risks, and managing consequences of
Read the full article at Venture in Security
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.