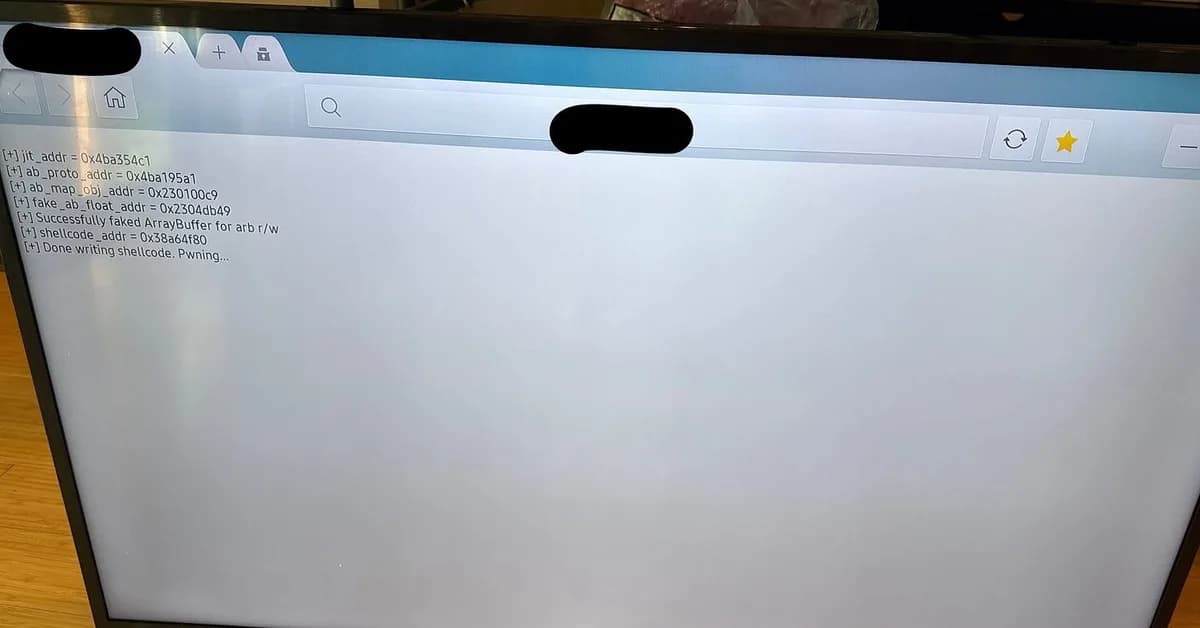
The detailed breakdown of how Codex exploited a Linux kernel vulnerability in a Tizen-based device to achieve privilege escalation is quite insightful. Here's a summary and analysis of the key steps:
Key Vulnerabilities Identified
-
Unvalidated Physical Memory Mapping via
ntksys:- The driver interface
/dev/ntksysallows user space to set physical memory ranges without proper validation. - This enables an attacker to map arbitrary physical addresses into their process's address space.
- The driver interface
-
Physical Address Leak via
ntkhdma:- Another device node,
/dev/ntkhdma, provides a way for unprivileged processes to obtain the physical address of a DMA buffer. - This helps in testing and validating the memory mapping functionality.
- Another device node,
Proof-of-Concept (PoC) Development
- Leak Physical Address:
- Codex developed a small Python script (
rmem.py) that interacts with/dev/ntkhdmato obtain a physical address of a DMA buffer.
python1python3 rmem.py ntkhdma_leak 2HDMA buffer phys addr: 0x84840000 - Codex developed a small Python script (
Read the full article at Malware Analysis, News and Indicators - Latest topics
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.
![[AINews] The Unreasonable Effectiveness of Closing the Loop](/_next/image?url=https%3A%2F%2Fmedia.nemati.ai%2Fmedia%2Fblog%2Fimages%2Farticles%2F600e22851bc7453b.webp&w=3840&q=75)



