A comprehensive guide to cryptography for software developers has been published, covering essential concepts and best practices. The article begins by defining cryptography as the practice of securing communication from adversaries through the use of codes.
Key points discussed include:
-
Hashes and Digests: These are used to verify data integrity without fully encrypting it. Cryptographic hash functions produce a fixed-size output (fingerprint) that ensures data has not been tampered with. Examples like SHA-256, BLAKE-2, MD5, and SHA-1 were mentioned, but MD5 and SHA-1 are deprecated due to security vulnerabilities.
-
Message Authentication Codes (MACs): MACs ensure both the integrity and authenticity of a message by using a shared secret key between sender and receiver. This is crucial for verifying that messages have not been altered in transit and come from an expected source.
-
Digital Signatures: Similar to MACs but use asymmetric cryptography, where the sender signs with their private key and the recipient verifies with the public key. This method does not require a shared secret beforehand.
-
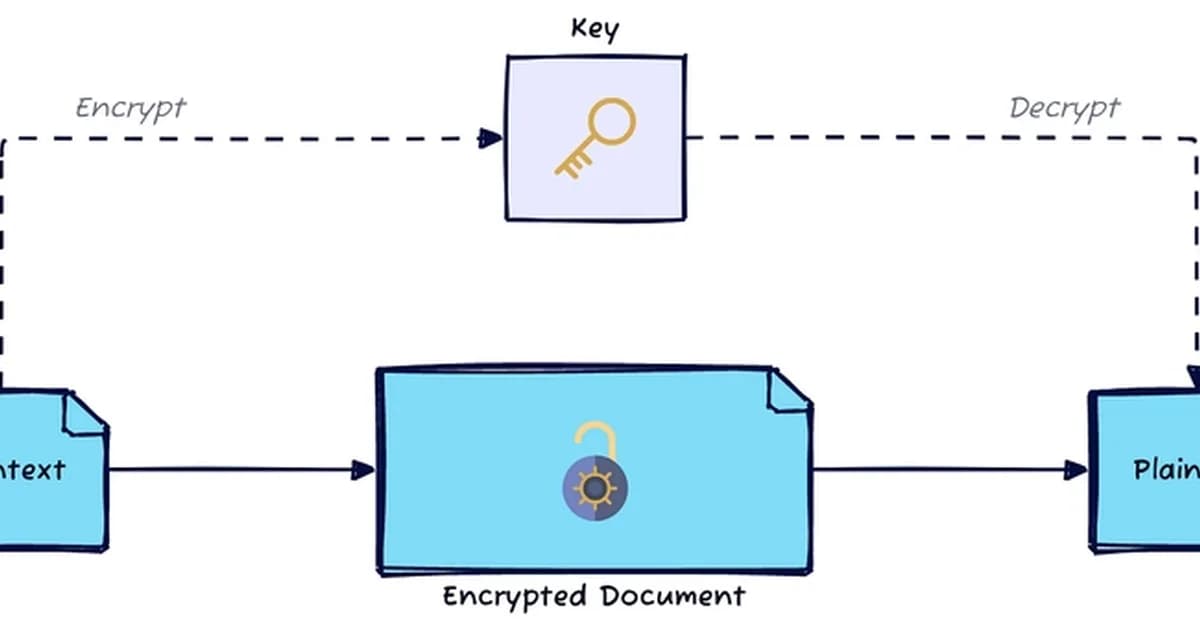
Symmetric vs Asymmetric Cryptography:
- Symmetric Cryptography (MACs): Uses a single key
Read the full article at DEV Community
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.
![[AINews] The Unreasonable Effectiveness of Closing the Loop](/_next/image?url=https%3A%2F%2Fmedia.nemati.ai%2Fmedia%2Fblog%2Fimages%2Farticles%2F600e22851bc7453b.webp&w=3840&q=75)



