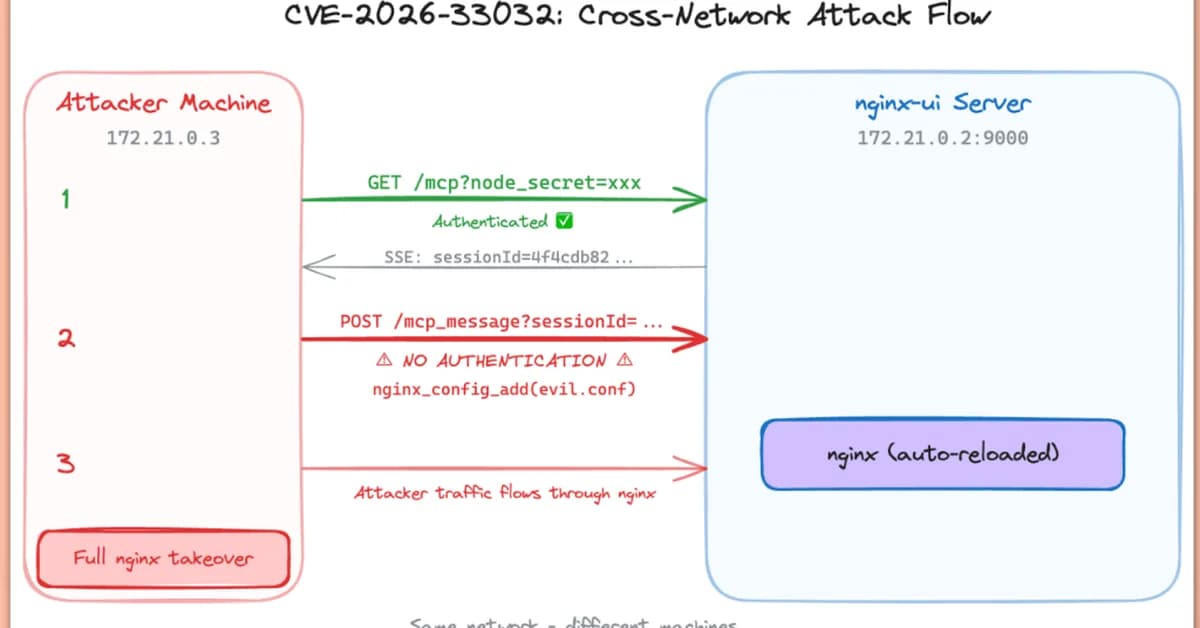
A critical vulnerability in nginx-ui (CVE-2026-33032) is being exploited to allow attackers unauthenticated access and full control over Nginx servers. This flaw, stemming from improper protection of the /mcp_message endpoint, poses a significant risk as it enables attackers to execute commands without authentication, compromising server security. Developers must urgently update to nginx-ui version 2.3.4 to mitigate this severe threat.
Read the full article at Security Affairs
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.
![[AINews] The Unreasonable Effectiveness of Closing the Loop](/_next/image?url=https%3A%2F%2Fmedia.nemati.ai%2Fmedia%2Fblog%2Fimages%2Farticles%2F600e22851bc7453b.webp&w=3840&q=75)



