The article from Malwarebytes discusses a sophisticated Windows infostealer named NWHStealer that is being spread through various methods, including fake Proton VPN websites and gaming mods. Here are the key points:
Methods of Distribution:
- Fake Websites: The malware spreads via fake Proton VPN setup pages (e.g.,
vpn-proton-setup[.]com). - GitHub and SourceForge: Malicious versions of software tools are uploaded to platforms like GitHub and SourceForge.
- YouTube Links: Downloads from links in YouTube video descriptions.
Infection Chain:
- Initial Download: Users download infected archives from trusted or fake websites.
- DLL Injection: The malware injects a DLL into processes like
RegAsm.exefor execution. - Process Hollowing: Uses low-level APIs to perform process hollowing and execute payloads in memory.
Payload: NWHStealer
- Data Collection: Enumerates cryptocurrency wallets, browser data, saved passwords, and other sensitive information.
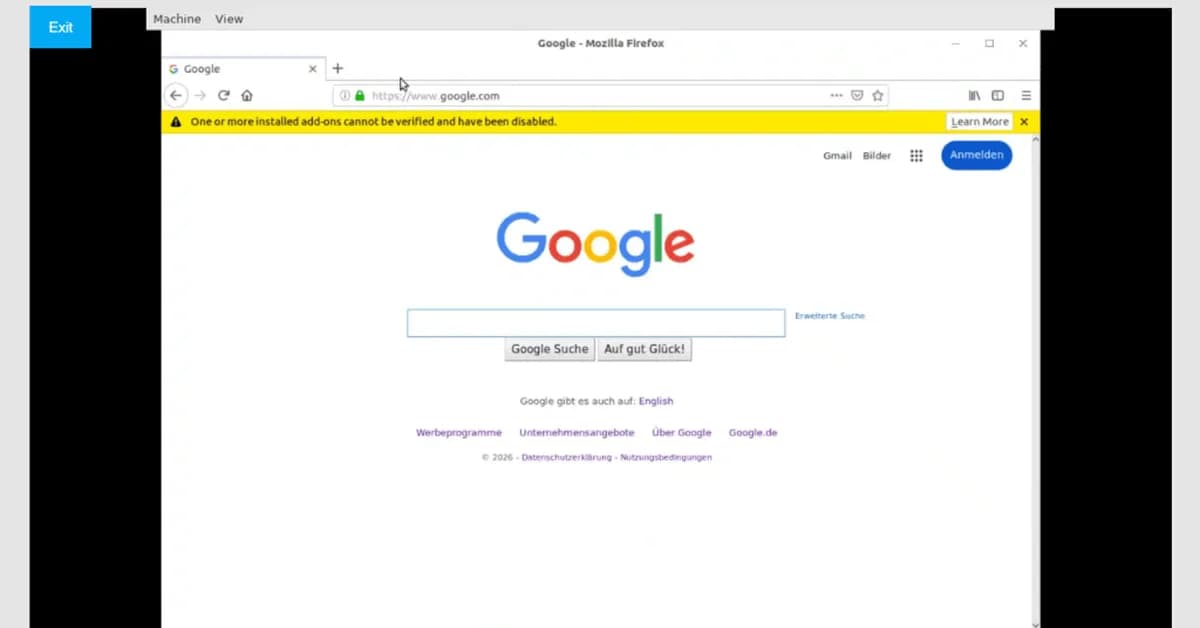
- Injection into Browsers: Injects a DLL into browser processes (e.g.,
msedge.exe,firefox.exe) to extract and exfiltrate data. - **Encryption
Read the full article at Malware Analysis, News and Indicators - Latest topics
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.
![[AINews] The Unreasonable Effectiveness of Closing the Loop](/_next/image?url=https%3A%2F%2Fmedia.nemati.ai%2Fmedia%2Fblog%2Fimages%2Farticles%2F600e22851bc7453b.webp&w=3840&q=75)



