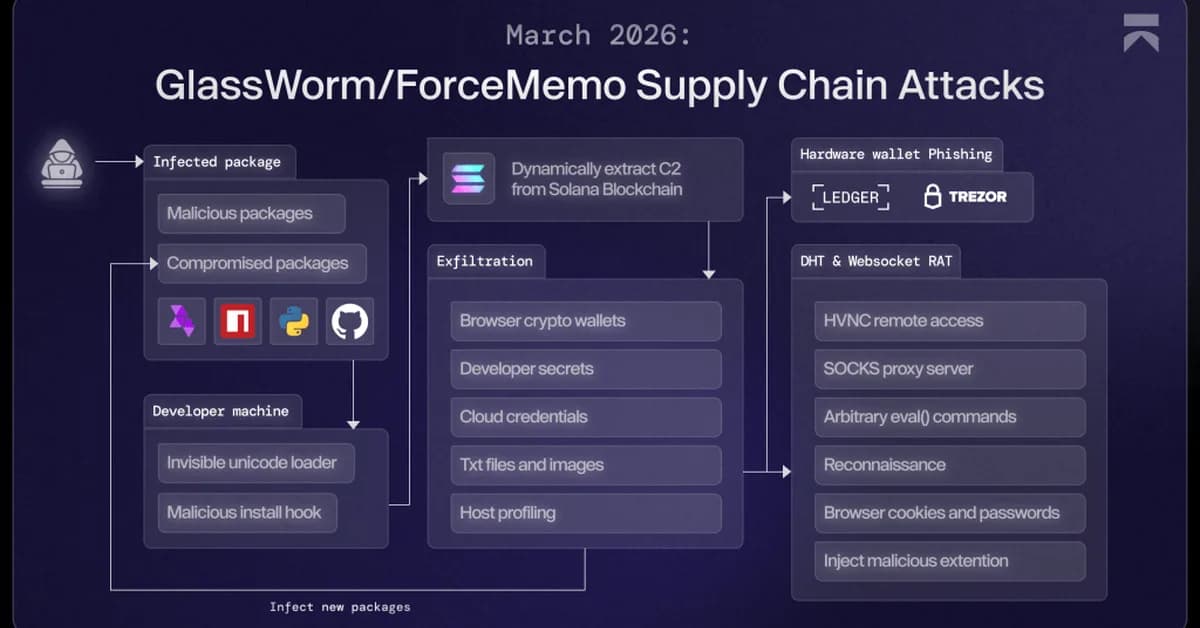
The GlassWorm campaign has evolved to use a Zig-based dropper in fake IDE extensions, compromising multiple developer tools and systems. This development is concerning for developers as it demonstrates sophisticated supply chain attacks that can infect entire ecosystems of integrated development environments with remote access trojans. Tech professionals should monitor their systems for suspicious extensions like 'code-wakatime-activity-tracker' or 'floktokbok.autoimport'.
Read the full article at Security Affairs
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.