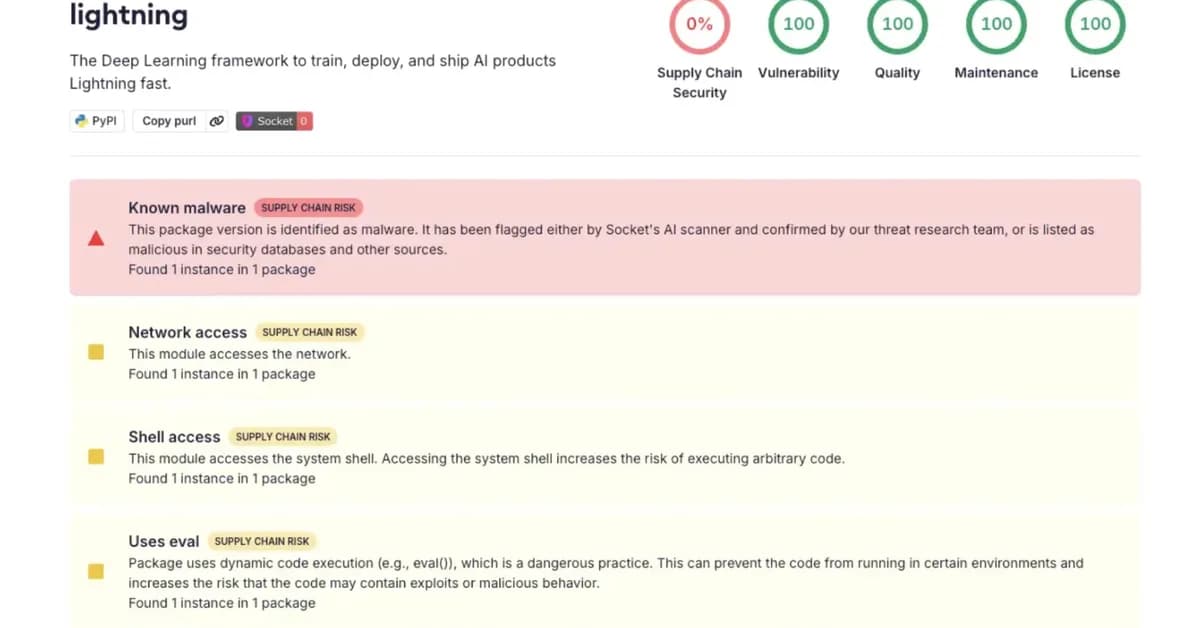
A security researcher exploited a vulnerable Google Cloud Storage bucket used for Helm binary distribution, simulating supply chain attacks that affected thousands of servers across various organizations. This incident highlights critical vulnerabilities in CI/CD pipelines and underscores the importance of secure software delivery practices. Developers must now prioritize rigorous audits and secure configurations to prevent similar breaches.
Read the full article at InfoSec Write-ups - Medium
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.