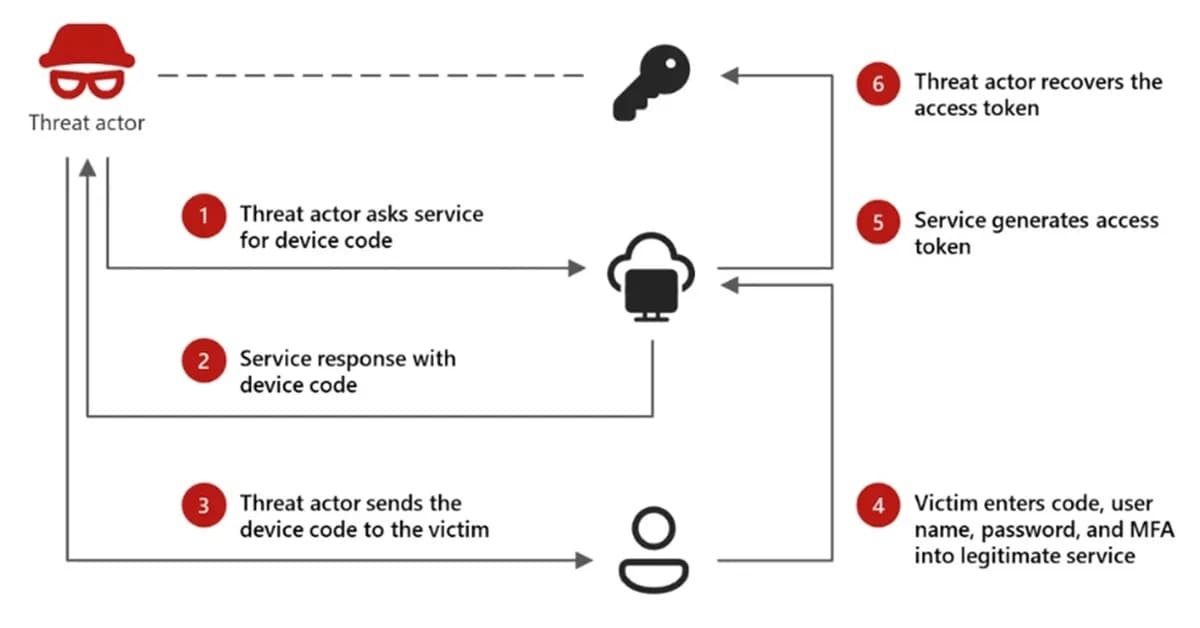
Microsoft Defender Security Research has identified a sophisticated phishing campaign that uses dynamic device code generation to bypass time constraints in OAuth 2.0 flows, enhancing attack success rates. This campaign leverages AI for personalized email content and real-time code generation, ensuring the generated codes remain valid until user interaction.
This development underscores the need for advanced security measures such as multi-factor authentication and continuous monitoring of account activities to mitigate risks associated with these evolving threats.
Read the full article at Malware Analysis, News and Indicators - Latest topics
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.
![[AINews] The Unreasonable Effectiveness of Closing the Loop](/_next/image?url=https%3A%2F%2Fmedia.nemati.ai%2Fmedia%2Fblog%2Fimages%2Farticles%2F600e22851bc7453b.webp&w=3840&q=75)



