The investigation into the evolving tactics of Triad Nexus (TN) highlights significant advancements in their infrastructure management, particularly concerning automated failover mechanisms, new naming schemas for CNAMEs, and continued exploitation of reputable cloud service providers. Here are key insights from the analysis:
Automated Failover Mechanisms
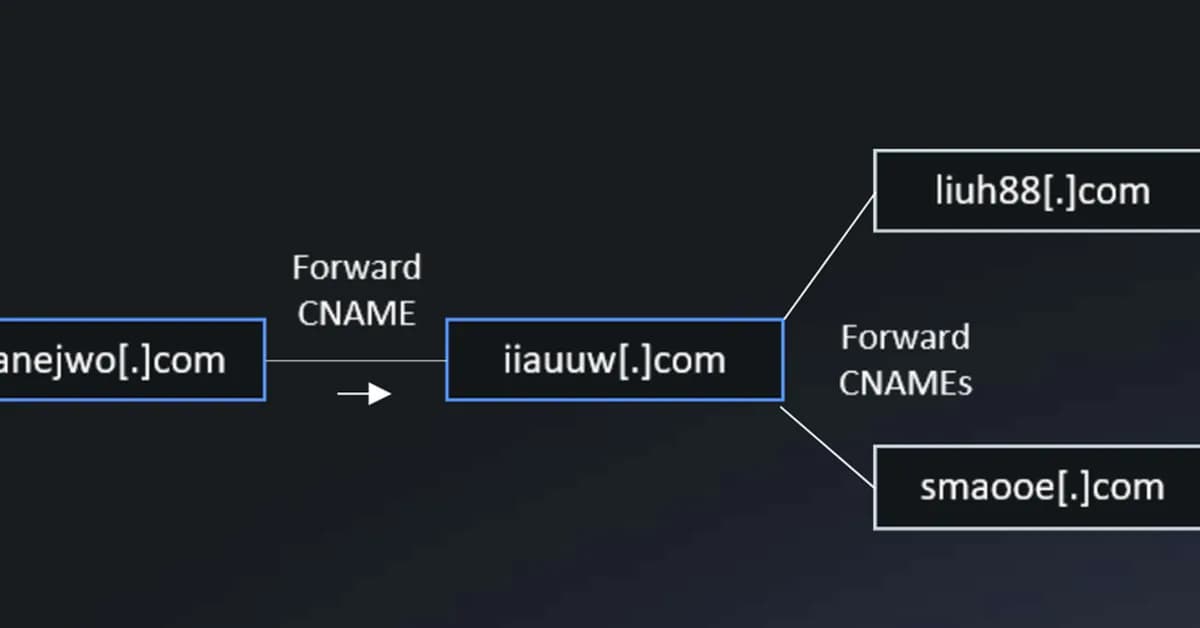
Triad Nexus has implemented sophisticated automation to rapidly switch between different IP addresses sourced from various ASNs (Autonomous System Numbers). This dynamic switching ensures that their infrastructure remains operational even when individual IPs or ASN-based services become compromised or flagged by security measures. For instance, CNAME domains like smaooe.com and ddge.ru have been observed rapidly cycling through multiple IP addresses across different cloud providers.
New Naming Schemas for CNAMEs
TN has shifted away from using recognizable patterns such as "FUNNULL" in their CNAME names to more generic or impersonating labels. This obfuscation makes it harder for security teams and researchers to identify TN's infrastructure at a glance. For example, cdn899.com and dnycdn.com are designed to blend into the background of legitimate DNS records.
Infrastructure Laundering
TN continues to exploit the reputations of major cloud service providers by
Read the full article at Malware Analysis, News and Indicators - Latest topics
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.
![[AINews] The Unreasonable Effectiveness of Closing the Loop](/_next/image?url=https%3A%2F%2Fmedia.nemati.ai%2Fmedia%2Fblog%2Fimages%2Farticles%2F600e22851bc7453b.webp&w=3840&q=75)



