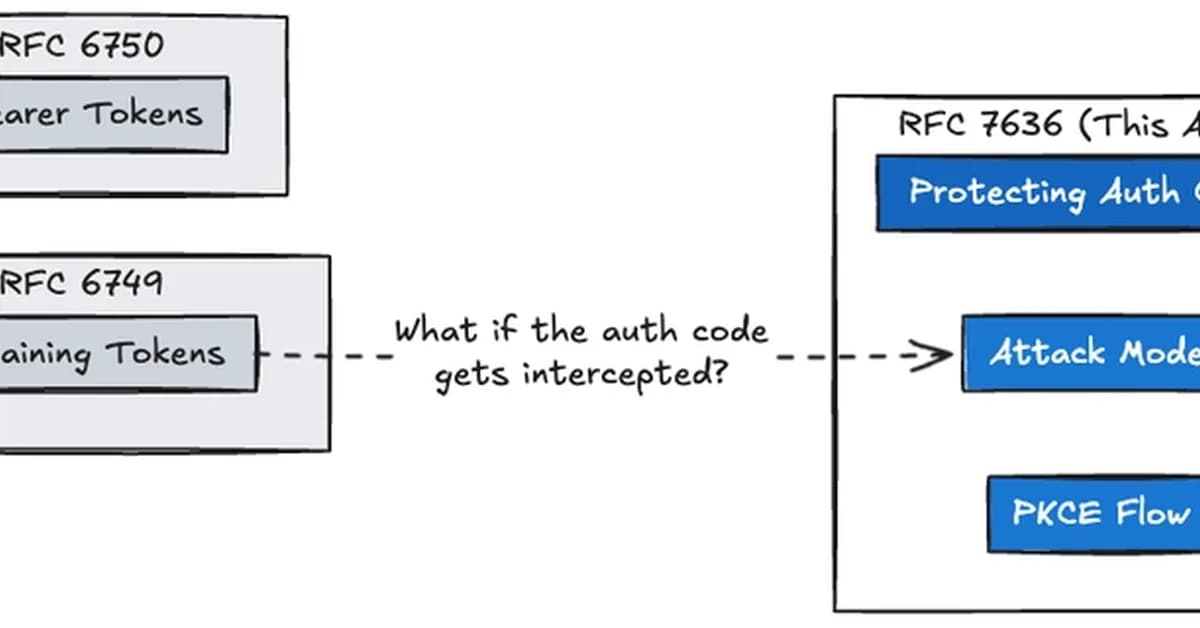
Summary of RFC 7636: Proof Key for Code Exchange (PKCE)
RFC 7636, titled "Proof Key for Code Exchange by OAuth Public Clients," addresses a critical security vulnerability in the OAuth 2.0 protocol, particularly when using authorization codes with public clients like native mobile and desktop applications.
Problem Addressed
- Custom URI Schemes: Native apps often use custom URI schemes (e.g.,
myapp://callback) for redirecting back to the app after an authentication flow. - Security Vulnerability: Any application can register a custom URI scheme, making it easy for attackers to intercept authorization codes and exploit them.
Solution: PKCE
PKCE introduces a mechanism to secure the delivery of authorization codes by using a mathematical secret (the code_verifier) that only the request initiator knows. This ensures that even if an attacker intercepts the authorization code, they cannot use it without knowing the corresponding code_verifier.
Key Components:
- Code Verifier: A cryptographically strong random string generated by the client.
- Code Challenge: The SHA-256 hash of the
code_verifier, which is sent to the authorization server during
Read the full article at DEV Community
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.
![[AINews] The Unreasonable Effectiveness of Closing the Loop](/_next/image?url=https%3A%2F%2Fmedia.nemati.ai%2Fmedia%2Fblog%2Fimages%2Farticles%2F600e22851bc7453b.webp&w=3840&q=75)



