Based on the detailed analysis of Storm-1175's tactics, techniques, and procedures (TTPs) in conducting ransomware attacks, here are key mitigation measures to defend against such threats:
1. Perimeter Security
- External Vulnerability Scanning: Utilize tools like Microsoft Defender External Attack Surface Management to identify and remediate vulnerabilities in web-facing systems.
- Network Isolation: Ensure critical servers are isolated from the public internet with secure network boundaries, using virtual private networks (VPNs) for access. Consider deploying web application firewalls (WAFs), reverse proxies, or perimeter networks if certain services must be publicly accessible.
2. Patch Management
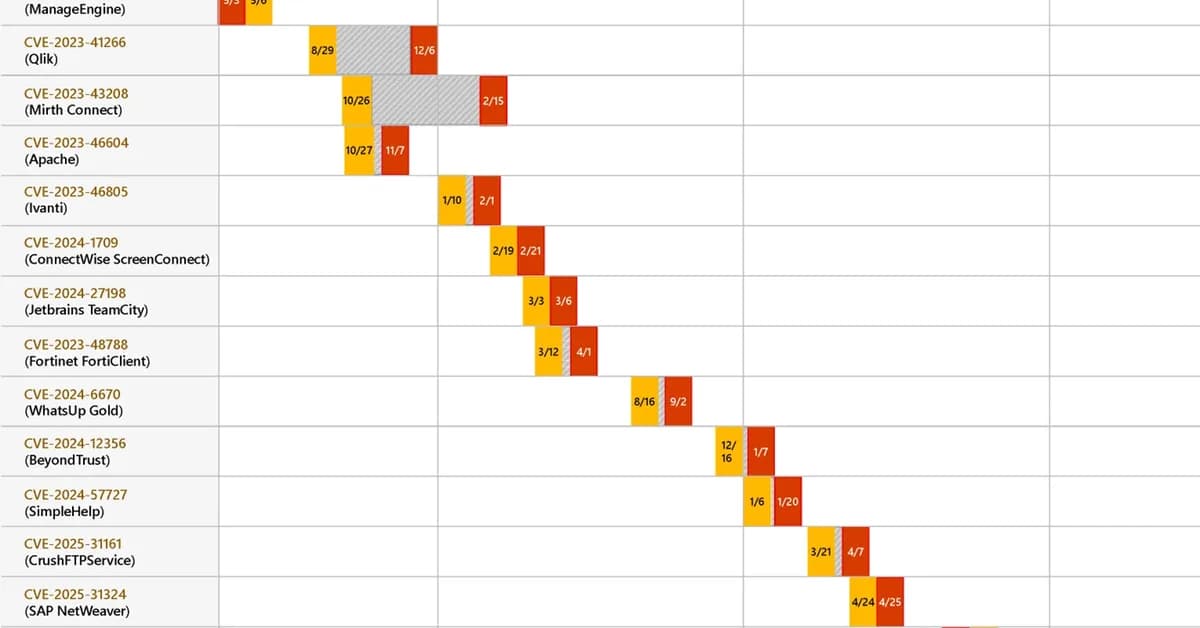
- Regular Patching: Implement a robust patch management process to address known vulnerabilities in software and systems.
- Critical Updates: Prioritize the installation of critical security updates for web-facing applications and infrastructure components.
3. Credential Hardening
- Least Privilege Principle: Enforce least privilege access controls, limiting administrative privileges to only necessary users and processes.
- Password Policies: Implement strong password policies and enforce regular password changes.
- Local Admin Rights Management: Restrict the
Read the full article at Malware Analysis, News and Indicators - Latest topics
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.
![[AINews] The Unreasonable Effectiveness of Closing the Loop](/_next/image?url=https%3A%2F%2Fmedia.nemati.ai%2Fmedia%2Fblog%2Fimages%2Farticles%2F600e22851bc7453b.webp&w=3840&q=75)



