The provided content outlines critical security measures and best practices for securing VMware vSphere environments against advanced threats. Here's a summary of the key points:
Security Measures
1. Implementing Multi-Factor Authentication (MFA)
- Control: Real-time alert on SSO account actions.
- Purpose: Prevents compromised Active Directory credentials from granting full access to vCenter.
2. Least Privilege Principle
- Control: Verify user roles and limit membership in specific groups like "BashShellAdministrators."
- Purpose: Reduces the risk of privilege escalation by ensuring that only necessary permissions are granted, even for administrative accounts.
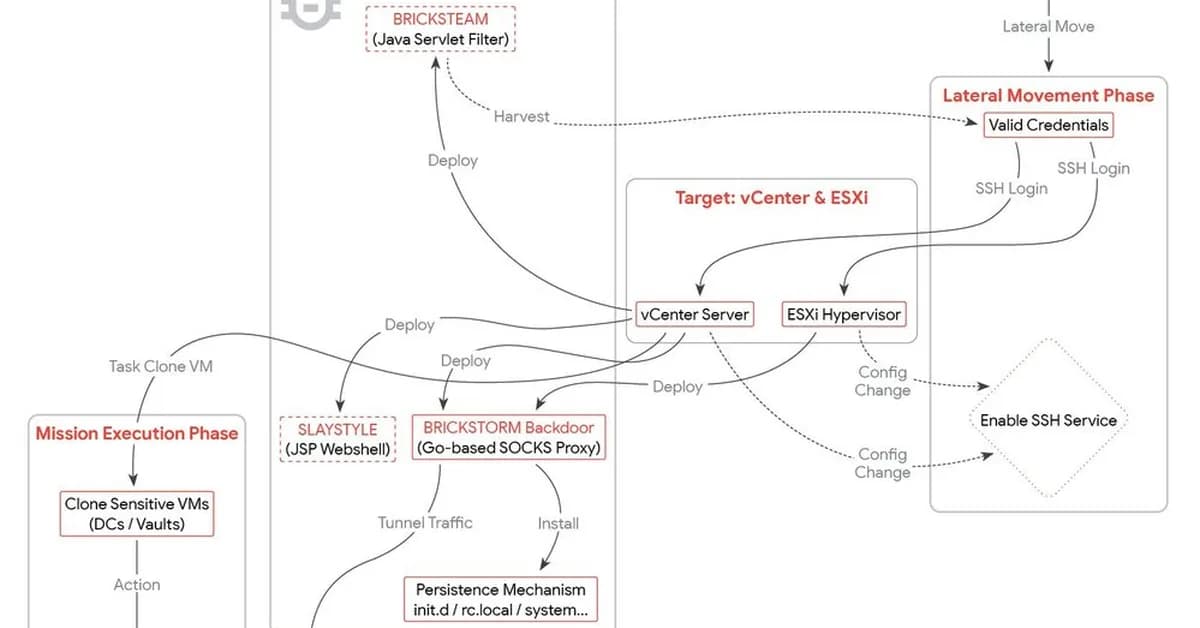
3. Disabling Unnecessary Services
- Control: Disable SSH enablement.
- Purpose: Prevents attackers from enabling SSH via VAMI (Port 5480) to deploy backdoors or gain unauthorized access.
Data Exfiltration Prevention
1. Transitioning Access Control Models
- From Permissive Model: Standard vSphere configurations often allow high-risk permissions like VM cloning and exporting within generalized administrative roles.
- To Cryptographic Enforcement Policy: Implement a comprehensive policy that enforces strict cryptographic controls to prevent
Read the full article at Threat Intelligence
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.
![[AINews] The Unreasonable Effectiveness of Closing the Loop](/_next/image?url=https%3A%2F%2Fmedia.nemati.ai%2Fmedia%2Fblog%2Fimages%2Farticles%2F600e22851bc7453b.webp&w=3840&q=75)



