The primary reason behind the transition to shorter-lived certificates in the SSL/TLS industry is due to the inherent weaknesses and limitations of current revocation mechanisms, particularly OCSP (Online Certificate Status Protocol). Here are the key points that explain this shift:
-
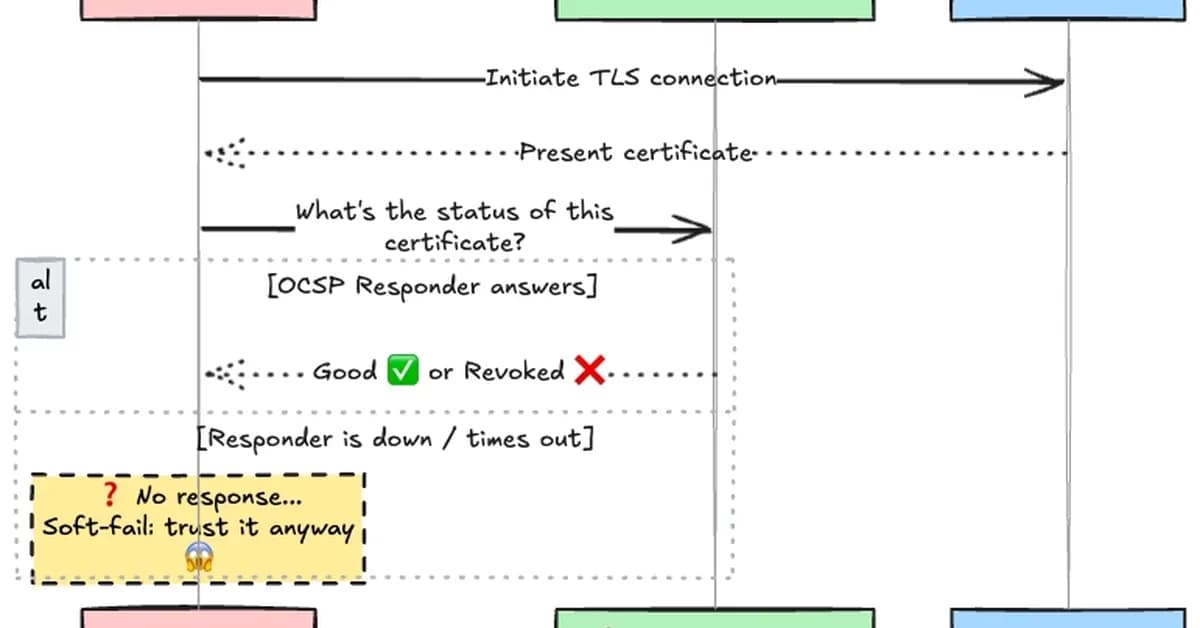
Revocation Mechanisms Are Broken: Traditional methods like CRLs (Certificate Revocation Lists) and OCSP suffer from scalability issues, privacy concerns, and reliability problems. For instance:
- CRLs can become too large to distribute efficiently.
- OCSP checks are prone to network latency and failures, making real-time revocation impractical.
-
Browser Vendors' Response: Major browsers have moved away from relying on OCSP for certificate validation due to these issues:
- Chrome: Discontinued real-time OCSP checks in 2012.
- Firefox: Implemented CRLite, a compressed revocation database using Bloom filters.
- Safari: Uses an Apple proprietary OCSP proxy but still faces privacy concerns.
-
Shorter Certificates as a Solution: Given the unreliability of revocation mechanisms:
- Shortening certificate lifetimes ensures that even if a private key is compromised, the
Read the full article at DEV Community
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.
![[AINews] The Unreasonable Effectiveness of Closing the Loop](/_next/image?url=https%3A%2F%2Fmedia.nemati.ai%2Fmedia%2Fblog%2Fimages%2Farticles%2F600e22851bc7453b.webp&w=3840&q=75)



