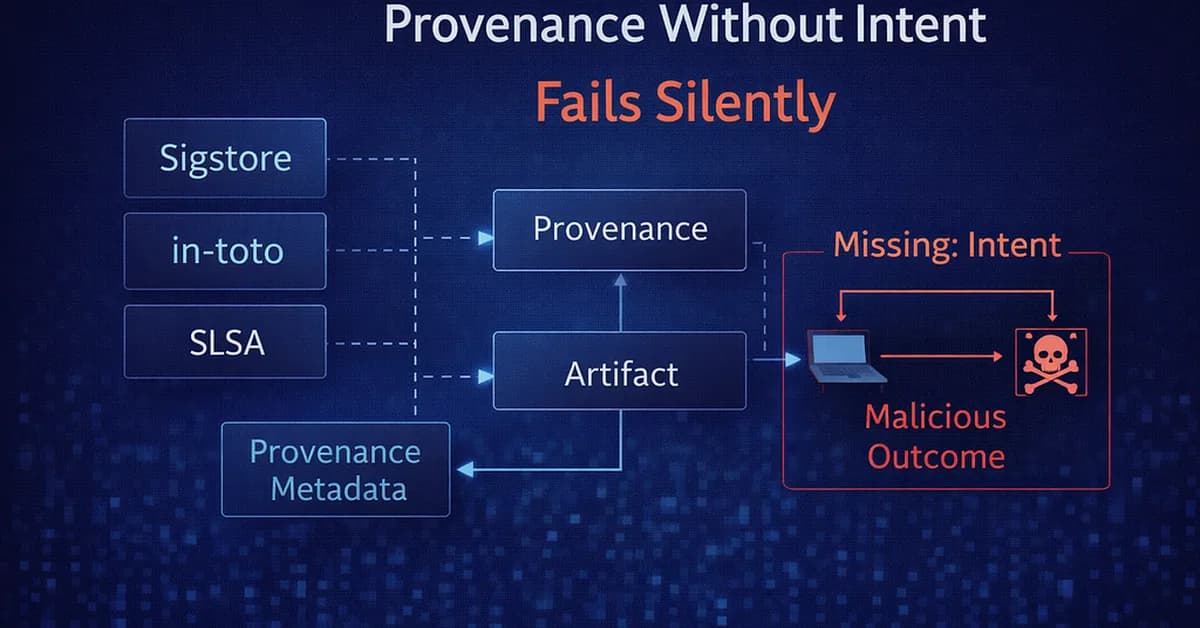
Modern supply-chain security frameworks like Sigstore, in-toto, and SLSA enhance artifact signing, provenance metadata, and policy enforcement but fail to verify human intent behind actions. This oversight allows attackers to manipulate compliant pipelines for malicious purposes, underscoring the need for an additional governance layer that ensures per-action human approval and physical separation of execution from approval processes.
Read the full article at System Weakness - Medium
Want to create content about this topic? Use Nemati AI tools to generate articles, social posts, and more.